Internal infrastructure penetration testing
Our internal infrastructure penetration testing goes beyond surface-level assessments, delivering expert-driven insights into your network’s weaknesses.
What is internal infrastructure penetration testing?
Internal infrastructure penetration testing is ethical hacking of the internal Windows (usually) network infrastructure that belongs to an organisation.
An internal penetration test evaluates the security of your internal infrastructure. It simulates scenarios where an attacker has already breached your network, looking for vulnerabilities to exploit. These attackers could be internal (e.g., unhappy employees) or external actors who have gained access through vulnerabilities, malware, or stolen credentials.
Key aspects of internal penetration testing include the ability to target internal networks, hosts, applications, or a combination of these based on specific needs, and the role of testers to identify access points and attempt lateral movement within the environment.
Why do you need an internal network infrastructure pentest?
When attackers target an organisation, their goal is to gain access to its internal network, either by breaching the perimeter or through social engineering tactics like phishing. Once inside, they attempt to reach the organisation’s most valuable assets—the “crown jewels”—by moving through the network, compromising accounts and systems along the way.
An internal infrastructure penetration test assesses how well your network is protected from an attacker who has already gained a foothold. It reveals how easily an attacker could navigate through your network, steal data, or take control of critical systems.
The benefit of this test is that it allows ethical hackers to safely uncover vulnerabilities and identify paths to critical assets, giving you the opportunity to fix weaknesses before malicious attackers exploit them. Without penetration testing, you increase your risk of security breaches that can result in financial losses and severe reputational damag
Ready to experience the future of pentesting?
Discover how combining expert insight with automation leads to faster, more precise, and high-impact penetration testing.
Crest-accredited internal infrastructure pentesting
Why Trust OnSecurity with your web application pentesting? Because we’re CREST-approved, adhering to the highest industry standards. Our CREST certification isn’t just a badge—it’s your assurance of top-tier security:
- Our methodologies, processes, and procedures undergo rigorous external vetting.
- Our pentesters are CREST-certified, having demonstrated their expertise through stringent assessments.
- We employ a best-in-class, manual-first approach to uncover vulnerabilities that others might miss.
Choose OnSecurity for unmatched excellence and thorough protection for your web applications.

Internal network security challenges
Securing your internal infrastructure presents unique challenges that require specialised knowledge and proactive measures:
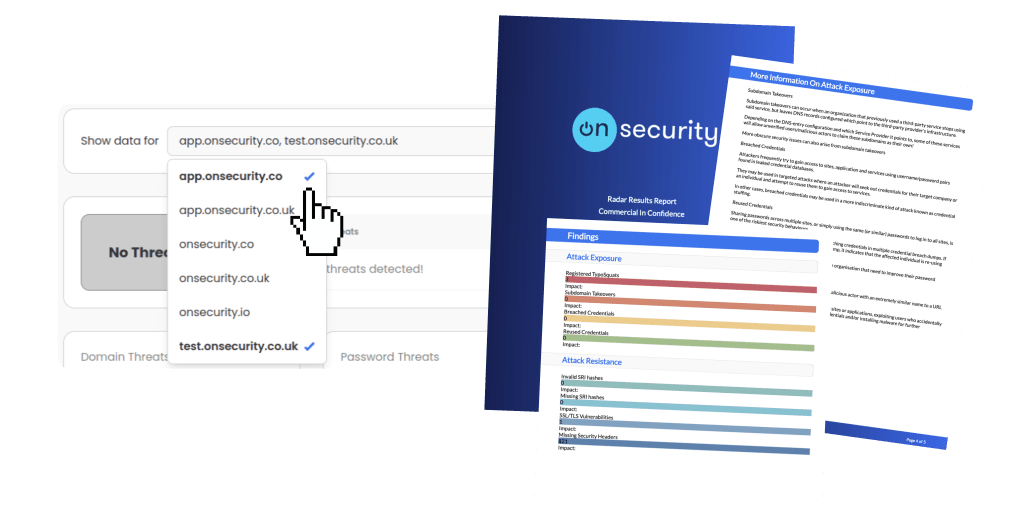
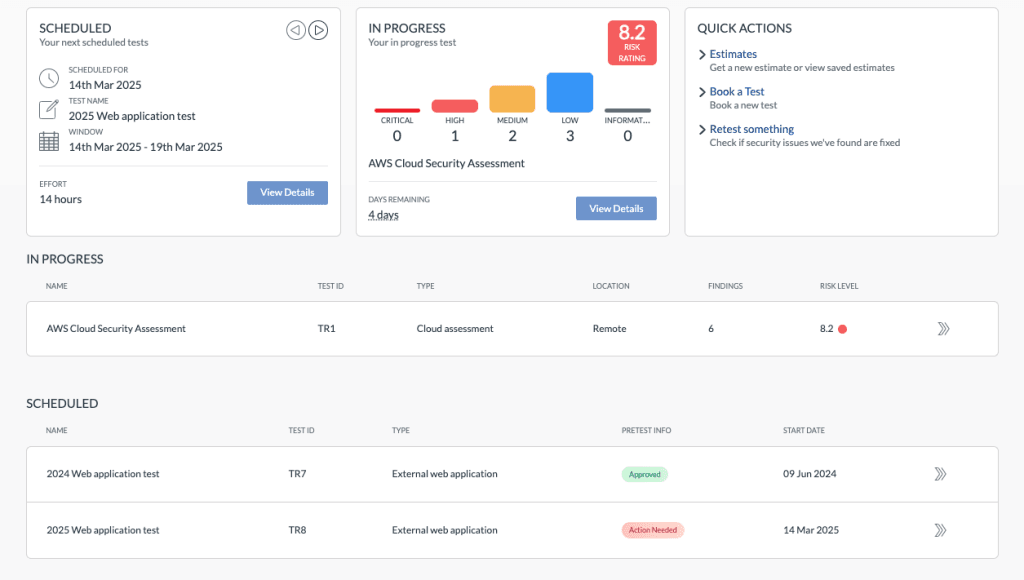
Quick, high-quality pentests
Discover why our user-friendly platform and AI + human approach make pentesting hassle- free.
Flexible subscription plans
Simplify your testing and monitoring with a single monthly payment, combining regular penetration tests and continuous vulnerability scanning. Get predictable costs while receiving ongoing protection.
Instant quote & customised plans
Receive a real-time, personalised cost estimate through our intuitive platform. Tailor your testing needs with configurable options that suit your business goals and security requirements.
Effortless platform access
No more long scoping processes. Book tests directly through our platform or get personalised assistance from our sales team. Enjoy streamlined communication and automated workflow notifications for maximum efficiency.
Immediate, actionable reports
Access your findings instantly through our platform. Generate detailed reports at any time, offering both technical insights and high-level summaries—without the wait.
Free retests for resolved issues
Once you’ve addressed vulnerabilities, we’ll retest them for free within a flexible window, ensuring your systems remain secure at no additional cost.
Ongoing protection & threat intelligence
Sign up for continuous monitoring to access automated vulnerability scanning, along with situational awareness through threat intelligence, ensuring your defences stay up to date year-round.
Other Types of penetration testing
Find the penetration test to best suit your business and cybersecurity needs.
Frequently Asked Questions
Got a question you need answering? Our FAQs should help guide you
Internal infrastructure penetration testing focuses on detecting vulnerabilities within an organisation’s internal network, simulating scenarios where an attacker has already gained access. In contrast, external penetration testing targets outward-facing systems, such as web servers and firewalls, to simulate attacks from outside the network perimeter. Internal tests assess risks after a breach, while external tests aim to prevent initial intrusions.
The length of time for each internal pen test can vary. We can provide a tailored estimate for the time needed for your internal penetration test following two straightforward scoping questions. This gives us a chance to evaluate the complexity of the environment and the size and functionality of your target.
An internal infrastructure penetration test should typically be conducted at least once a year. However, more frequent testing may be necessary if there are significant changes to the network, such as system upgrades, new applications, or after a security breach. Plus if your organisation has strict regulatory requirements or high-security environments to adhere to, it may benefit from conducting tests more regularly, such as quarterly or biannually, to ensure continuous protection against evolving threats.
Our testers keep you informed with updates during the testing process, delivering notifications directly to your workflow apps as vulnerabilities are uncovered. This ensures you're aware of any issues as they arise, without having to wait for the final report to take action.
Our experienced professionals conduct penetration tests with precision and care, ensuring no major disruption to your operations. We offer the flexibility to perform tests in UAT, staging, or development environments to further reduce any impact. Throughout the process, we provide continuous updates, enabling you to swiftly address any security concerns as they are identified.
Our internal penetration test provides valuable insights, including a detailed account of how vulnerabilities were combined to compromise your network, an overview of the main vulnerabilities discovered, information on weak passwords cracked, and details on service misconfigurations. Most importantly, we provide actionable recommendations to fix these issues and prevent real-world attackers from exploiting them.
Regular infrastructure penetration testing is a crucial part of any organisation's cybersecurity strategy. We recommend conducting a comprehensive test, covering both internal and external networks, at least once a year. In addition, it's important to perform relevant tests before launching any new systems, following significant changes to internal or external infrastructure, to ensure these assets don’t introduce new vulnerabilities.
Alongside penetration testing, we also advise continuous vulnerability scanning, and threat intelligence. Staying proactive with patch management and remediation is essential. If you have more questions to help select a reputable pen testing service, don’t hesitate to get in touch.