OnSecurity's Latest Articles, News and Industry Tips
Security should be important to everyone. Our blog features articles regarding your business’ security and different aspects to consider.
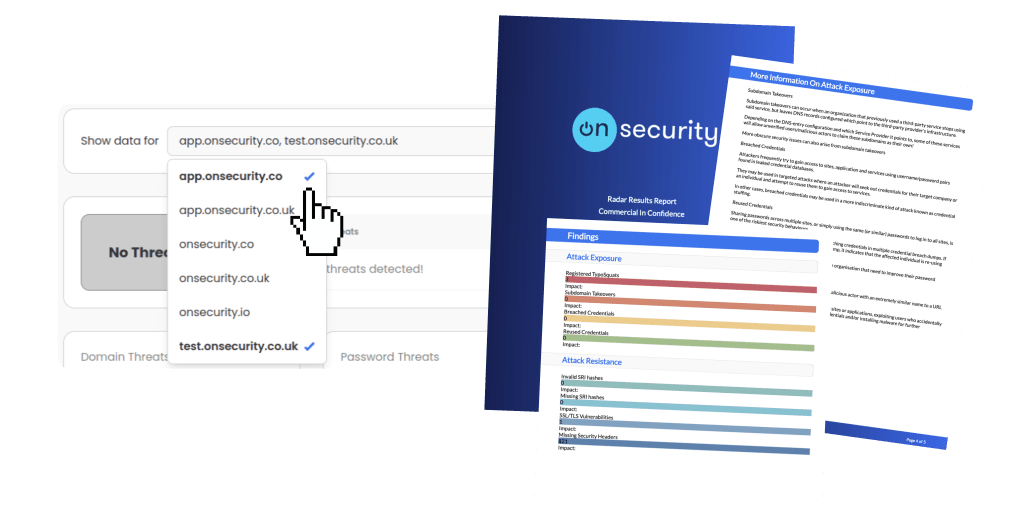
Ready to experience the future of pentesting?
Discover how combining expert insight with automation leads to faster, more precise, and high-impact penetration testing.