OnSecurity's Latest Articles, News and Industry Tips
Security should be important to everyone. Our blog features articles regarding your business’ security and different aspects to consider.

Cloud-native security systems are transforming the way businesses protect their digital assets. Built for the cloud, these systems offer dynamic and scalable solutions to defend against evolving threats. In this blog, we’ll explore what cloud-native security systems are and why they’re essential for modern businesses.
Penetration testing is a mostly manual process carried out by experienced consultants, using some of the same methods and tools a real hacker would. You decide on the scope of your test with your consultant, set your target, and your tester will get to work attempting to breach it. This blog will explore the importance of pentesting for businesses and how to begin.
What is social engineering? This blog will define what is meant by ‘social engineering’ in cybersecurity, providing a breakdown of the behavioural techniques that cybercriminals use to manipulate their victims into giving up confidential information or allowing hackers access to secure areas.
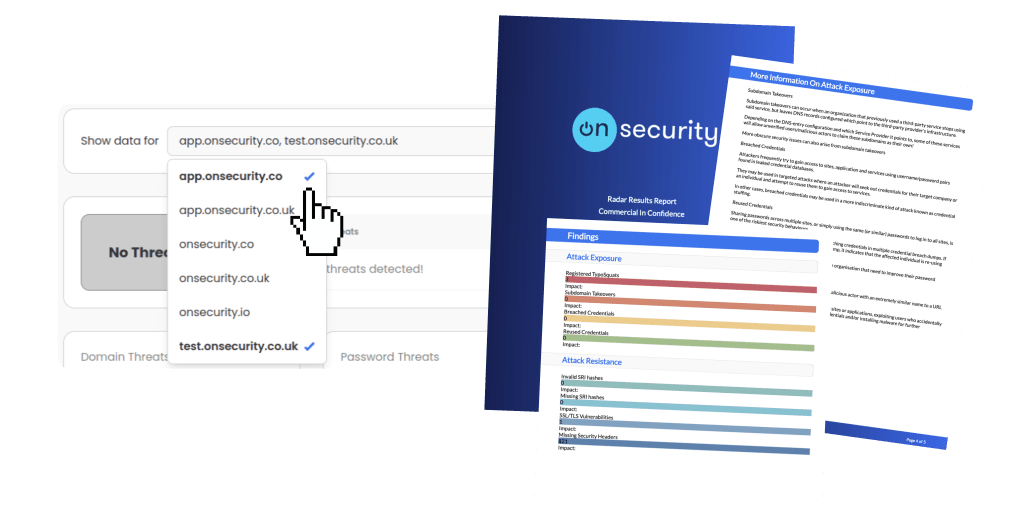
Ready to experience the future of pentesting?
Discover how combining expert insight with automation leads to faster, more precise, and high-impact penetration testing.