OnSecurity's Latest Articles, News and Industry Tips
Security should be important to everyone. Our blog features articles regarding your business’ security and different aspects to consider.

Cyber threats are evolving, and every business – large or small – faces potential risks. A single vulnerability in your network infrastructure can lead to data breaches, financial losses and reputational damage. Network penetration testing is a proactive approach to uncover and address these vulnerabilities.
Phishing emails are very common. They are spam emails that land in your inbox or junk folder that imitate a real-life, well-known company (or even someone you may know) and ask you to provide them with sensitive information. Be it usernames, passwords or card details, these cybercriminals will aim to get what they need to ‘hack’ you further and can cause many issues including financial loss.
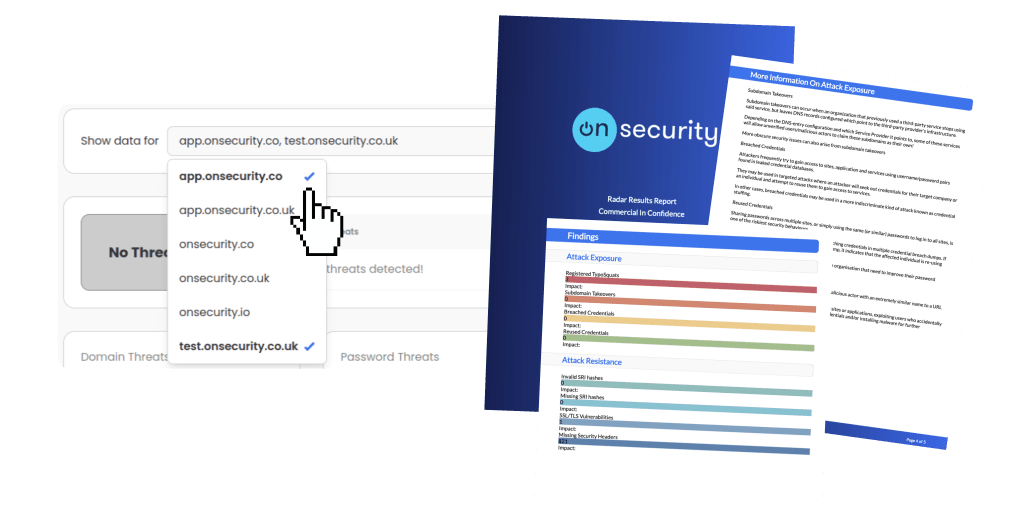
Ready to experience the future of pentesting?
Discover how combining expert insight with automation leads to faster, more precise, and high-impact penetration testing.