OnSecurity's Latest Articles, News and Industry Tips
Security should be important to everyone. Our blog features articles regarding your business’ security and different aspects to consider.

A practical guide to implementing Secure by Design in UK government product delivery. Covers risk-driven design, lifecycle security activities, compliance with the PSTI Act, and how regular penetration testing keeps your security posture continuously validated.

Cyber threats are evolving, and every business – large or small – faces potential risks. A single vulnerability in your network infrastructure can lead to data breaches, financial losses and reputational damage. Network penetration testing is a proactive approach to uncover and address these vulnerabilities.

Cloud-native security systems are transforming the way businesses protect their digital assets. Built for the cloud, these systems offer dynamic and scalable solutions to defend against evolving threats. In this blog, we’ll explore what cloud-native security systems are and why they’re essential for modern businesses.
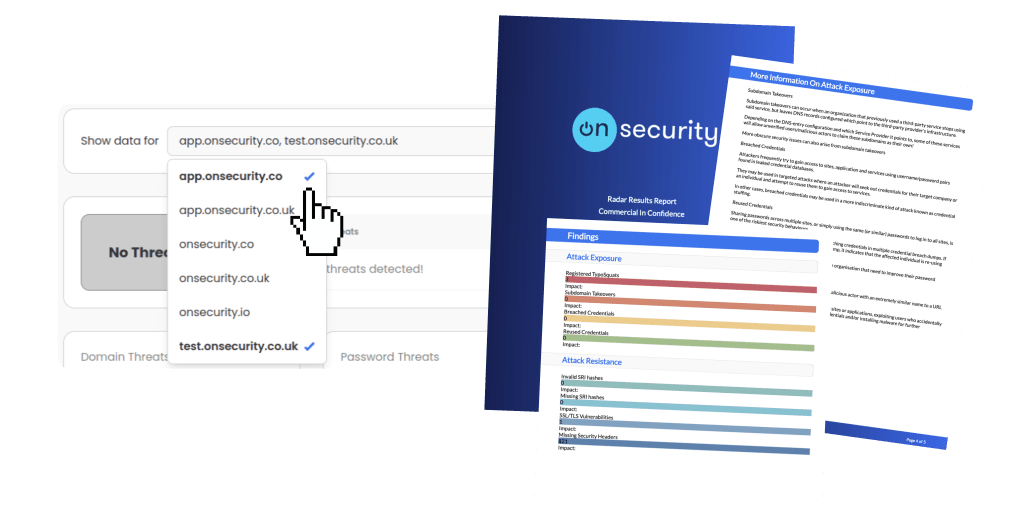
Ready to experience the future of pentesting?
Discover how combining expert insight with automation leads to faster, more precise, and high-impact penetration testing.