OnSecurity's Latest Articles, News and Industry Tips
Security should be important to everyone. Our blog features articles regarding your business’ security and different aspects to consider.

News and Industry Trends
A practical guide to implementing Secure by Design in UK government product delivery. Covers risk-driven design, lifecycle security activities, compliance with the PSTI Act, and how regular penetration testing keeps your security posture continuously validated.
26 February 2026
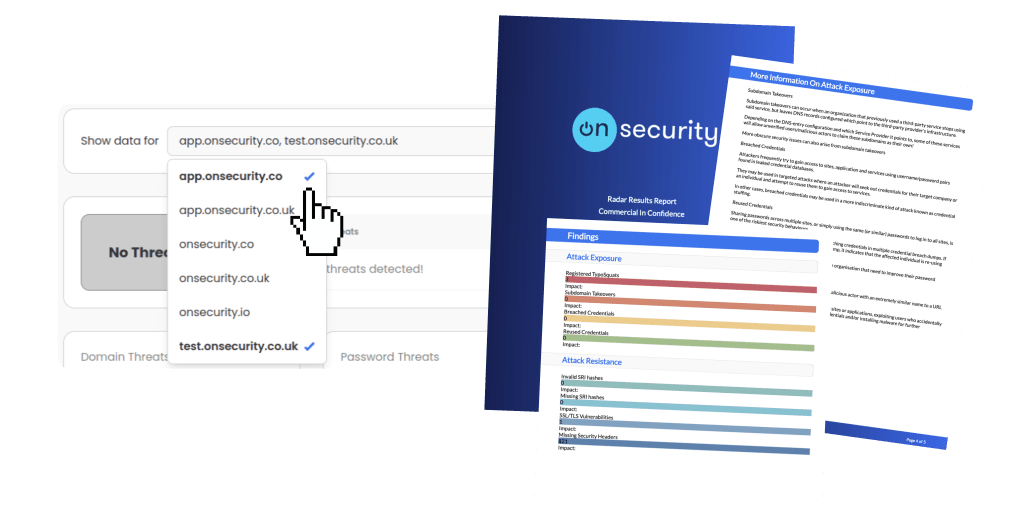
Ready to experience the future of pentesting?
Discover how combining expert insight with automation leads to faster, more precise, and high-impact penetration testing.