OnSecurity's Latest Articles, News and Industry Tips
Security should be important to everyone. Our blog features articles regarding your business’ security and different aspects to consider.

A practical guide to implementing Secure by Design in UK government product delivery. Covers risk-driven design, lifecycle security activities, compliance with the PSTI Act, and how regular penetration testing keeps your security posture continuously validated.

OnSecurity’s Pentest Files uncovers the latest vulnerabilities and real-life remediation steps to prevent businesses from malicious attack. In this article we find out how our Head of Pentesting is able to hijack admin invitations to bypass the login wall in our clients infrastructure.
What is social engineering? This blog will define what is meant by ‘social engineering’ in cybersecurity, providing a breakdown of the behavioural techniques that cybercriminals use to manipulate their victims into giving up confidential information or allowing hackers access to secure areas.
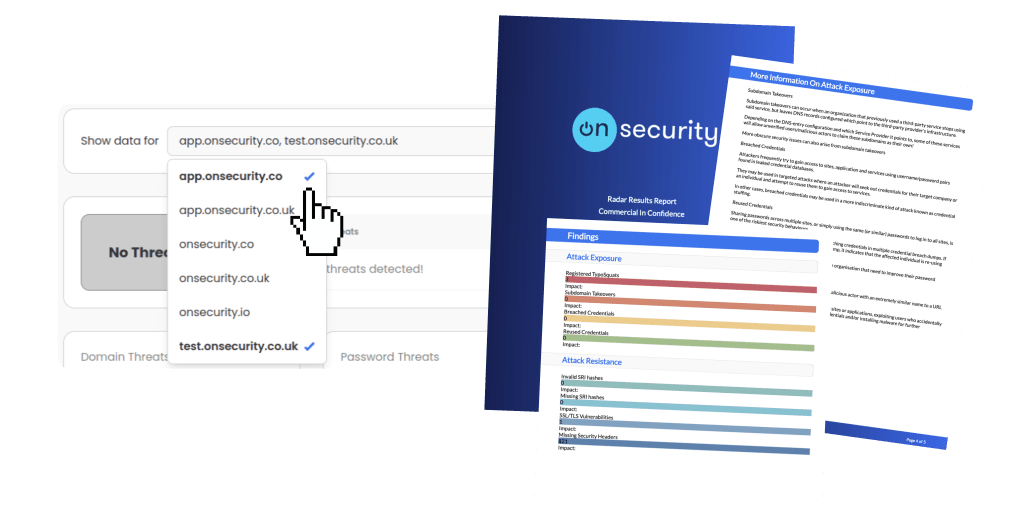
Ready to experience the future of pentesting?
Discover how combining expert insight with automation leads to faster, more precise, and high-impact penetration testing.