OnSecurity's Latest Articles, News and Industry Tips
Security should be important to everyone. Our blog features articles regarding your business’ security and different aspects to consider.

A practical guide to implementing Secure by Design in UK government product delivery. Covers risk-driven design, lifecycle security activities, compliance with the PSTI Act, and how regular penetration testing keeps your security posture continuously validated.

OnSecurity’s Pentest Files uncovers the latest vulnerabilities and real-life remediation steps to prevent businesses from malicious attack. In this article we find out how our Head of Pentesting is able to hijack admin invitations to bypass the login wall in our clients infrastructure.
Phishing emails are very common. They are spam emails that land in your inbox or junk folder that imitate a real-life, well-known company (or even someone you may know) and ask you to provide them with sensitive information. Be it usernames, passwords or card details, these cybercriminals will aim to get what they need to ‘hack’ you further and can cause many issues including financial loss.
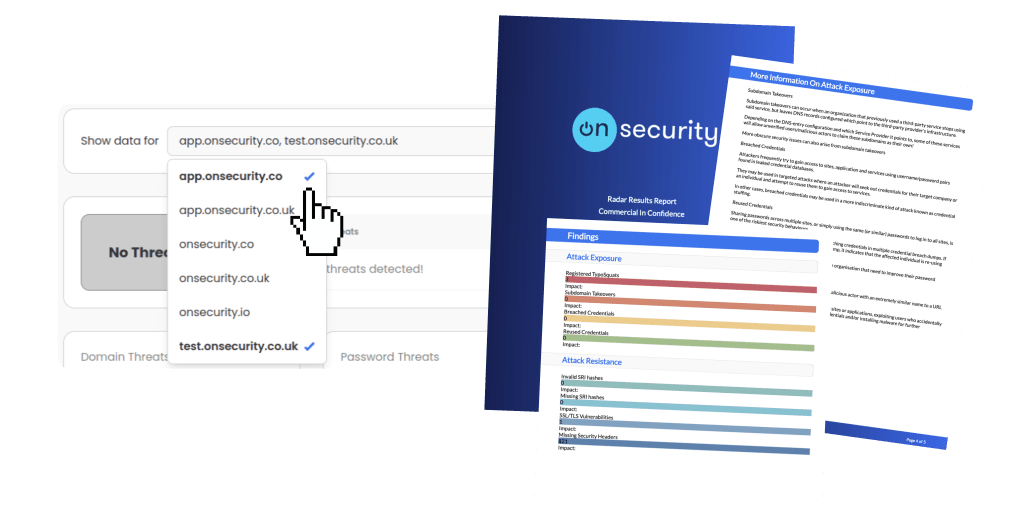
Ready to experience the future of pentesting?
Discover how combining expert insight with automation leads to faster, more precise, and high-impact penetration testing.